Oracle Cloud offers a pretty great free tier, which is super useful for hosting hobby and other projects. I wanted to set up a site-to-site VPN from home to the OCI resources so I could make pretty graphs and integrate them with some services I'm hosting from home without exposing all sorts of things to the public internet.
I have an Unifi network at home, which while I'm not in love with all the decisions they've made, I'm reasonably happy with and wanted to have it handle the tunnel and routing.
Unfortunately, all the documentation for OCI is for more enterprise-y solutions. It doesn't have specifics for Unifi and any results I dug up from Google were either incomplete, referencing previous and old UI (because if there's anything Ubiquity likes doing it's re-doing the UI repeatedly) and option names, or linked to documentation that no longer exists, both on the Oracle and Unifi side.
I did get it working, but due to the lack of documentation, it took rather longer than I would have liked, and figured I should share the journey with the next person who is trying to figure out what the problem is and what setting was overlooked.
The initial setup was pretty easy: Oracle offers a pretty straightforward VPN wizard you can run from their web UI, right from the management page for the site-to-site VPNs.
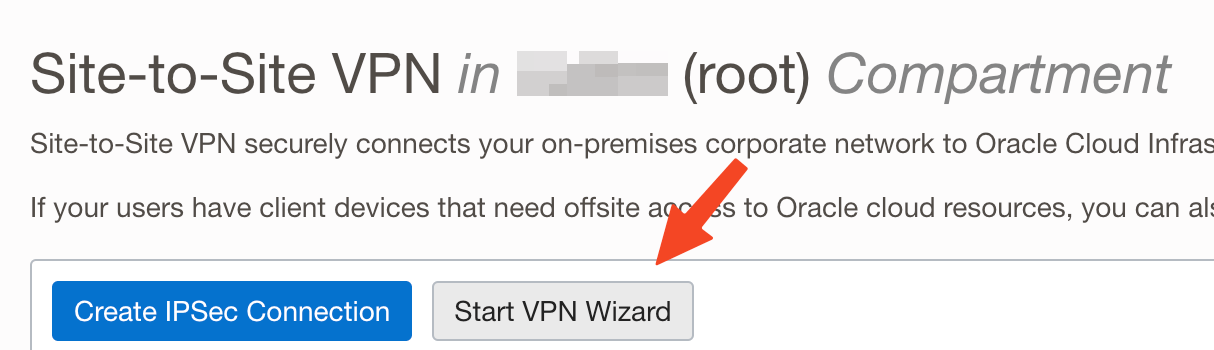
Follow that to its end, and you'll end up with a (mostly) working configuration, and it's pretty self-explanatory and all you're going to need is the IP addresses of your local/home/whatever network, and the public IP of the device that's going to initiate the tunnel.
Once you're done with the wizard, it'll create a new VPN with a pair of tunnels.
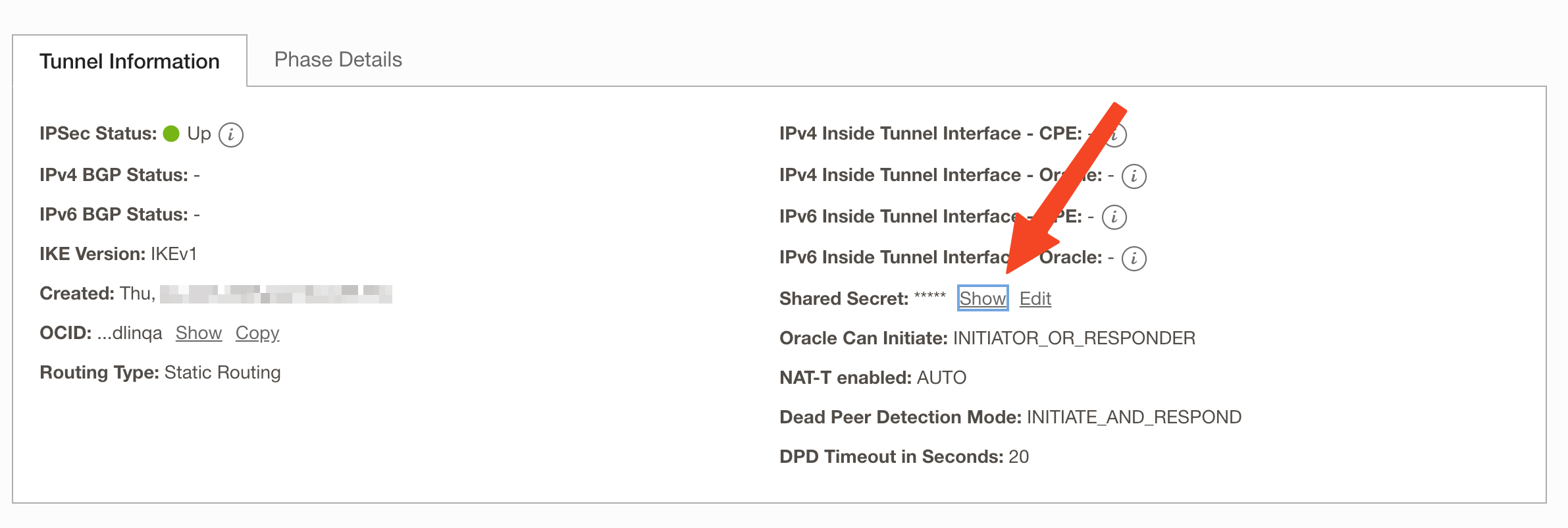
You'll then need to grab the shared key for the Unifi setup, as well as the IP of the tunnel you'd like to use. I found a post from a while ago that due to how OCI balances traffic between both tunnels, they had an issue that required using the 2nd of the two provisioned tunnels for it to connect and pass traffic; I don't know if this is strictly necessary but it's how I configured my setup.
Click on the VPN name, and the VPN management page that shows up will list both tunnels, and the IP you need will be visible. For the key, click on the 2nd tunnel, and it'll be in the tunnel information box, called 'shared secret'.
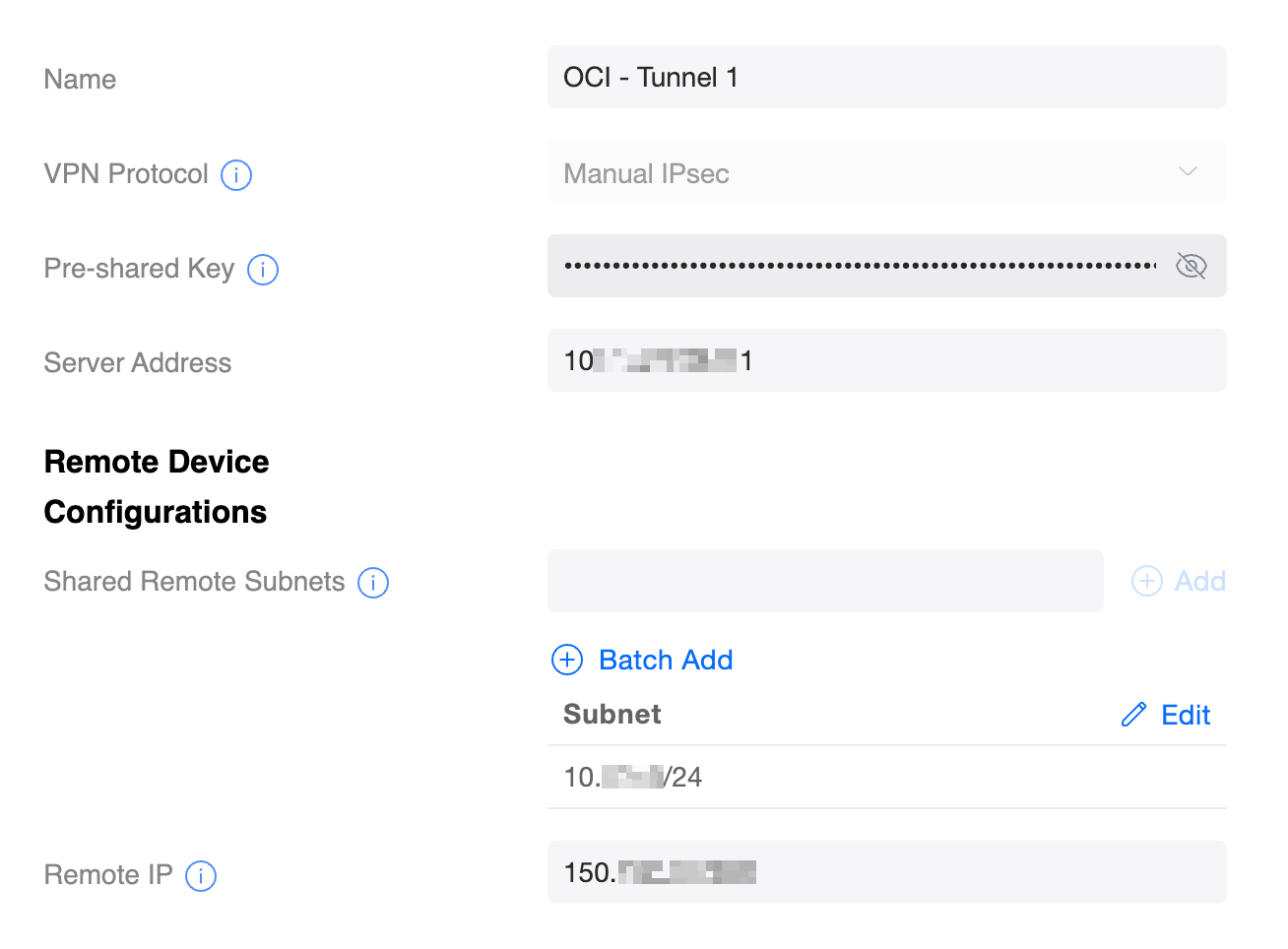
Once you have the IP and key, you're ready to head on over to your Unifi installer. I'm going to use screenshots from the 'new' UI, though all the options are present in the legacy UI and mostly in the same place, and all named mostly the same thing, so there's very little difference between the two.
In the new UI, it's clearly labeled as 'VPN', and you'll want to hit the 'Create Site-to-Site VPN' button, and give it a name, the shared secret in the pre-shared key field, and your local public IP in the Server Address. For the remote subnet, I added the VCN's subnet, and the remote IP is the tunnel's IP.
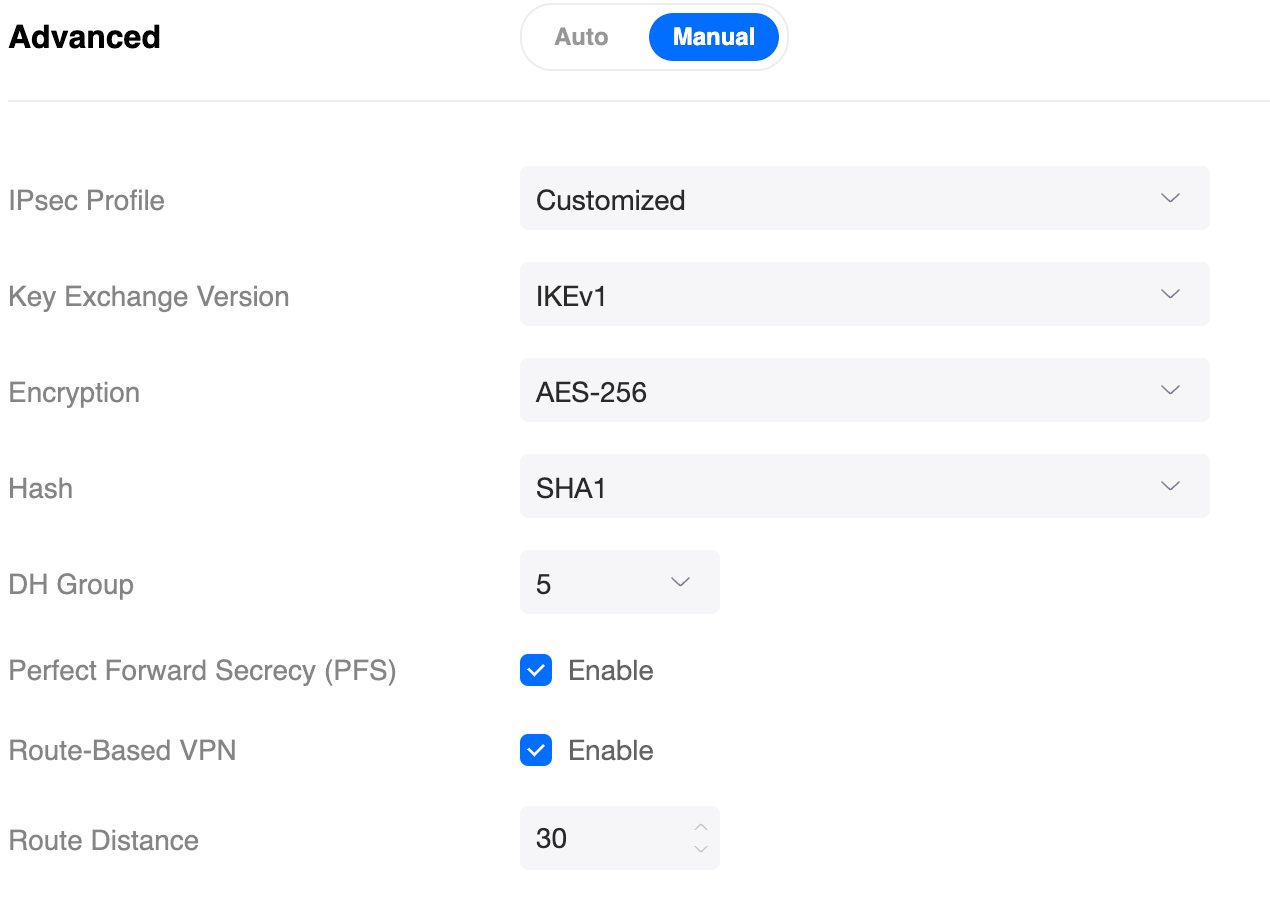
There are a couple of advanced settings you'll need to tweak, so change that to manual. You'll need to set the Encryption to AES-256, and the DH group to 5 as those are the default options on the OCI side, and both halves of the tunnel need to have matching settings.
Once you've done that, save it and give it a couple of minutes to see if the tunnel comes up; you can find the status in the OCI web UI: the little dot in the IPSec status for the tunnel will turn green once it's up.
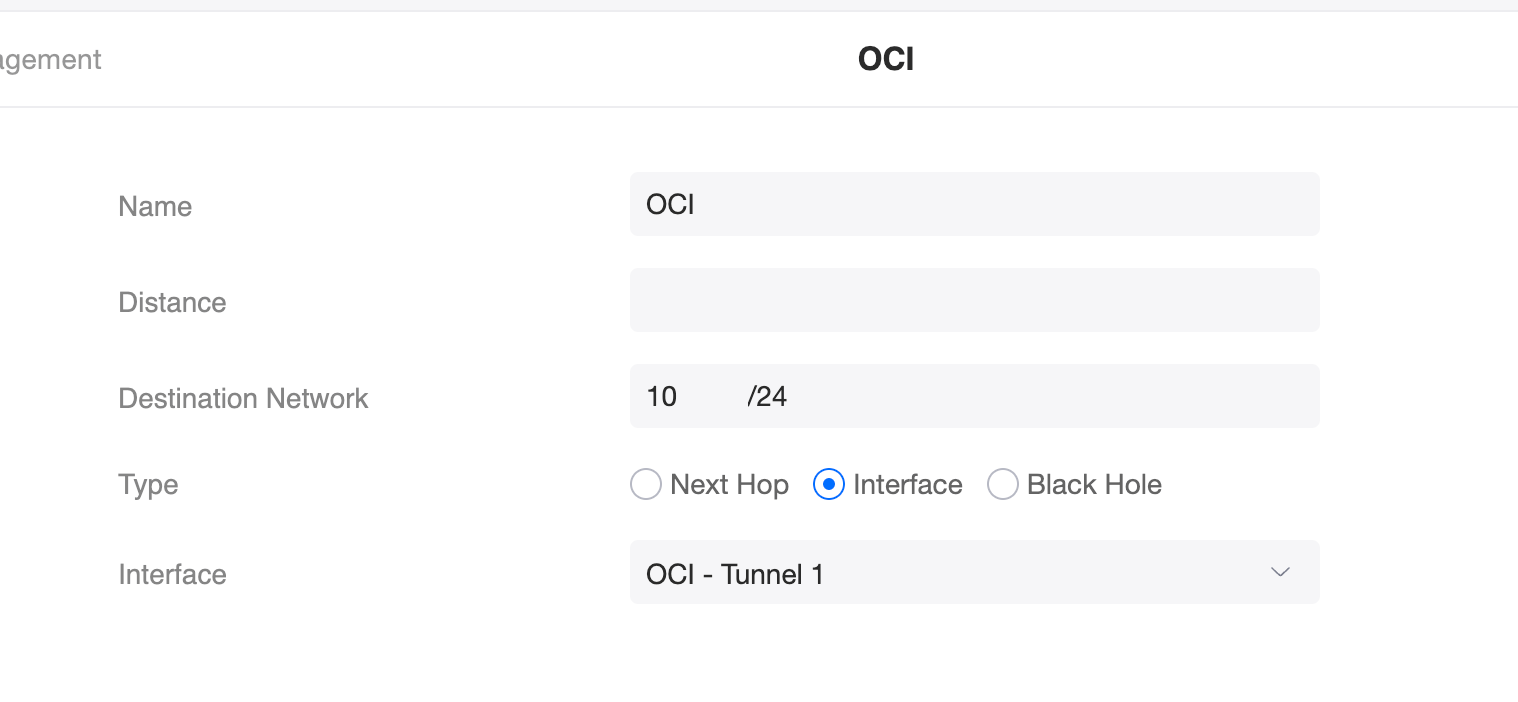
You'll also need to add a static route for the OCI subnet to your Unifi controller, assuming you want actually to pass traffic. It's under 'Traffic Management' and you want to add a new static route.
The Destination is the IPs of the subnet on your Oracle VCN you want to access remotely and set the type to Interface, and the Interface to the VPN tunnel you created.
If everything is correct, give it a couple of minutes and you should be able to access your remote resources, but keep in mind the traffic is still gated by any security policies on your VCNs, so things like pings and any ports you have not explicitly allowed will not work through the VPN so you may have to make changes if particular services or protocols don't work.
One thing that tripped me up was getting the static routes correct: the OCI side wants your local IP subnet - whatever your router is handing out to clients - and the Unifi wants the remote IP subnet - which is whatever is being assigned to your resources in the VCN.
Once I got the static routes right, everything just... works.
